Cyber Threats to the 2018 Winter Olympic Games
Written By: An IntelliGenesis Cybersecurity Analyst
Many of us took some time last month to cheer on the red, white, and blue as American athletes competed on the world stage. We felt a huge sense of pride as they donned old glory in victory during the 2018 Winter Olympics, hosted in Pyeongchang, South Korea. Historically, the Olympics have been the venue for hosting countries to showcase just how advanced they are with technology. Nearly 10 years ago, China used the 2008 Summer Olympics to boast how technologically advanced the China Next Generation Internet (CNGI) network was with its use of IPv6 during the games.

In 2012, London used technology to broadcast results and keep all of Britain up to speed with what was going on in the games. The use of mobile applications, social media, and BBC Big Screens kept everyone in the know, regardless of where they were. The BBC Big Screens are 275 sq. ft. LCD screens strategically placed in 21 cities across the United Kingdom to broadcast the events. This Olympic event was not different from the unveiling of South Korea’s use of 5G wireless technology and some cutting edge virtual reality.
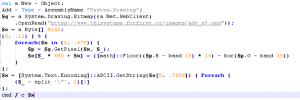

Maryland Representative Dutch Ruppersberger once said, “People ask me all the time, ‘What keeps you up at night?’ And I say, ‘Spicy Mexican food, weapons of mass destruction, and cyber attacks.'” These advances in technology also highlight how nearly everything in the Olympics is online and vulnerable to cyber threats. Hacking campaigns have been in full operation long before the opening ceremony and make use of known techniques and practices. One spear phishing campaign included emails sent to “icehockey@pyeongchang2018.com” with hundreds of other Olympics-related targets blind copied on the emails. The majority of these organizations had some association with the Olympics, either in providing infrastructure or in a supporting role. The email contained a Word document, which contained an obfuscated Visual Basic macro that launched a powershell script. The powershell script would then download and read an image file, from a remote location, that contained yet another hidden script. The script was embedded into the pixels of the image file in byte chunks. This technique of hiding data within null bits of a file has been around since 1985 and is called stenography. Once the script runs, it passes the decoded script from the image file to the command line to execute that actual implant script. The implant establishes an encrypted channel to the attacker’s server where the attacker would have full command and control over the victim’s computer. This spear phishing campaign may have only been the beginning of a much larger operation that could have devastated the critical infrastructure for the Olympics. A less-than-catastrophic threat to the infrastructure was realized in the opening ceremony when the wifi went down in the stadium and the IP televisions malfunctioned in the main press room. Also, the opening ceremony was supposed to be filmed by drones flying above and throughout the stadium but they would not launch. As a precaution, all of the servers were taken offline, leaving attendees unable to access their tickets from the Winter Olympics website. After analysis of the identified malware and compromised devices, security experts said that the attacker seemed to have pulled their punches, given the fact that with the level of access the attacker had and the potential to completely destroy the infected device. We can all speculate on the reason why, but the fact remains that the threat of cyber warfare is increasingly growing. Another threat that has been realized during the games has been the compromise of public wireless access points in the area and local hotels. These compromised access points have resulted in stolen login credentials, financial information, and other personally identifiable information for unknowing guests and VIPs from all around the world. I am sure that we will all see reflections of the compromises in the coming months and years as everyone goes home to their respective countries to give the cyber attacker an expanded global footprint.